October 21, 2021
VPN Protocols: A Complete Guide for 2025
The average VPN has at least a couple of VPN protocols on offer, but what’s the difference [...]
WHAT’S IN THIS REVIEW?
Disclaimer: Partnerships & affiliate links help us create better content. Learn how.
As with any leak, identifying the source is the first step to fixing the problem. Data leaks follow the same principle, and they’re simple to troubleshoot while using a VPN. A virtual private network (VPN) works to hide your IP address by switching it with an IP used by the VPN server you’ve connected to. While connected, you’ll benefit from increased anonymity, which helps you access blocked websites as well as improve your online privacy.
Given the sensitive nature of VPN use, data leaks need to be plugged in instantly. Otherwise, there’s no real point in using the service in the first place. There are various different data leaks to be aware of, whether it be DNS-related or your original IP address that is exposed for all to see.
Here’s everything you need to know about the different types of VPN data leaks, as well as step-by-step instructions detailing how to fix each of them.
A data leak can occur due to a variety of issues. With a VPN, it happens when the service exposes personal information that can be used to identify the user. Obviously, this defeats the purpose of using a VPN for privacy and needs to be fixed immediately. The method to do so will depend on the type of leak you’re experiencing as well as the VPN provider you’ve selected.
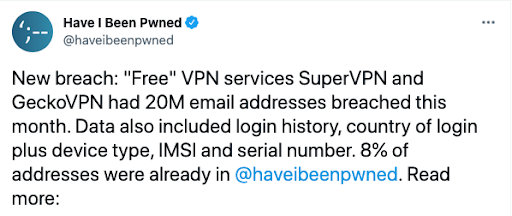
While most VPNs protect against the majority of data leaks, some are more effective than others. In that regard, we recommend avoiding the use of free VPN services given their history of being breached easily.
We’d also advise sticking with an audited provider that has the ability to either support or block IPv6 to avoid the need to plug leaks in the first place. A leak can spring if your connection drops suddenly, and there’s no kill switch enabled. Other examples would be if your VPN isn’t properly configured with your operating system (OS) or the protocol you’ve selected lacks proper protection measures. (Some VPN protocols are built for speed, while others focus on security.)
As for how to tell if there’s a leak, the first step is to see if the VPN is working as it should be. Here are the easiest and quickest ways to check for data leaks on your device:
Every internet connection comes with an Internet Protocol (IP) address. These are assigned by your internet service provider. An IP leak means that your real address is visible, and your VPN isn’t connecting to the server properly. The fix depends on which type of IP address has been assigned to the user.
The two variations of an IP address are IPv4 and IPv6. Initially, IPv4 was released back in the 1970s, and IPv6 launched in the 1990s to ensure the internet could continue expanding. (IPv5 was never properly implemented, so we’ll skip that altogether here).
IPv4 allows for roughly 4.29 billion internet addresses, and it’s no real surprise to learn that we’re running out. IPv6 increases the maximum available number of available addresses to 2128 (or 340 trillion trillion trillion). Try wrapping your brain around that.
Some providers still rely on the older tech, which is a clear risk from a simple numbers perspective. However, this doesn’t mean IPv6 is necessarily safer, as it may not be supported by VPNs in the first place.
The original and the easiest to troubleshoot, it’s unlikely that you’ll encounter an IPv4 leak while using a VPN. With that being said, it’s still possible. We’d recommend switching over to a different server location to see if it’s a problem with a specific region.
Otherwise, the best advice would be to switch to a better provider if you consistently face IPv4 issues. A VPN that can’t protect your data on an IPv4 protocol won’t be any good to you if privacy and data security is what you’re after.
Ideally, the VPN will support IPv6 or will block the connection. NordVPN is a good example of the latter, as they explain:
“In a nutshell, if a NordVPN customer were to have an IPv6 IP address, their IPv6 interface would be blocked and only IPv4 traffic would be rerouted and encrypted with NordVPN, which ensures that your real IP address never leaks.”
It’s a solid workaround that is likely to be implemented more in the future. Beyond that, the method to fix IPv6 data leaks depends on your OS.
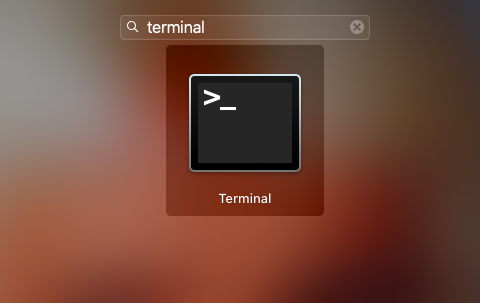
To disable IPv6 on macOS you’ll need to use the Terminal feature.
One route to do so is to navigate through:
Windows users can also turn off IPv6 via the Network/WiFi icon.
Mobile devices are a different story, and it doesn’t matter whether it’s Android or iOS. Apple’s “walled garden” makes it impossible to disable IPv6 without jailbreaking one of its devices, while you’ll need either root access or a third-party app to be able to do so with the Android OS.
Neither are great options from a security POV. For mobile devices, you’ll just have to hope that the VPN isn’t leaking data.
The internet domain name system (DNS) is how we match website names with IP addresses. Due to the nature of computing, every website has a real address which is actually a list of numbers. It would be impossible to remember any website using this method, so a DNS helps to translate a domain name that way you can reach a website using letters instead.
Normally, requests travel through the DNS server of your internet provider, which allows them to see everything you’re up to while you’re online. With a VPN, this traffic is redirected to anonymous DNS servers. (It’s also a great means to avoid ISP speed throttling.)
Therefore, a DNS leak is when your ISP is able to see the server request. You can check for a leak using a tool like DNSLeak.com or DNSLeakTest.com.
The best way to avoid DNS leaks is to stick with a provider that manages their own DNS server. This provides ample DNS leak protection, since they’re able to secure their own networks better than public channels. You could also look to a third-party tool for a fix, but it’s generally easier to simply use a VPN covering their own bases. This way you won’t suffer from the issue in the first place.
WebRTC stands for “Web Real-Time Communication”. It’s open-source technology that supports video, voice, and generic data sent between peers within a browser. A WebRTC leak occurs when your external IP address is exposed. It’s a vulnerability originating from the browser, rather than the VPN itself.
Here are a few browsers that can potentially be affected by WebRTC leaks:
WebRTC uses STUN (Session Traversal Utilities for Nat), a protocol that allows sites to discover the public IP address of a user. They’re also difficult to detect. The feature can be useful, but WebRTC STUN requests aren’t ideal if you’re using a VPN for privacy purposes.
We’d start by loading up ipleak.net/ while the VPN is active to check if you can see your ISP-assigned (external) IP address.
If you have identified a leak, there are a couple of solutions to choose from. You can either disable WebRTC directly in the browser or use a browser add-on/extension to do so. (Disabling it directly doesn’t always work depending on the browser you’re using.)
Here’s a rundown with fixes for the most popular browsers:

There are few downsides to torrenting, although your BitTorrent client could be leaking your IP address even if the VPN is working as it should be. Even if you stick to torrents of the legal variety, this isn’t ideal, as an ISP could throttle your download speeds if they’re able to detect what you’re doing. If you’re downloading illegal files, websites monitor thousands of copy-infringing torrent swarms worldwide and publish the IP addresses of peers. For many reasons, it’s advised that you don’t do this.
TCP and UDP are the two ways in which a torrent IP leak can occur. The two protocols are used when downloading a torrent file, and there’s a fix for each one.
If you’ve started downloading a torrent before connecting to a VPN, this is likely to be the source of your TCP leak (Transmission Control Protocol). The easiest fix is to remove the torrent file, close the BitTorrent client, connect to the VPN, and start again.
The IPv4/IPv6 issue might rear its head once more, so look for an option to enable IPv6 Protection if the VPN has the ability to do so. Finally, head to the BitTorrent client’s connection settings menu, and deactivate any proxy settings.
In comparison to TCP, UDP leaks (User Datagram Protocol) are rare to encounter. The methods mentioned above should help to fix any issues, although it is possible that your VPN might not support UDP whatsoever.
In that case, we’d look to a superior VPN service that is able to handle torrents.
There are various additional steps you can take to preemptively plug any potential leaks.
A kill switch is one of the easiest ways to ensure that no data will be shared if the VPN cuts off unexpectedly. It’s a simple feature, but one that should be enabled at all times if you’re serious about maintaining online privacy.
Many providers offer this feature as part of their service including NordVPN, IPVanish, and PureVPN. To learn more about each, check out their plans and in-depth VPN reviews below.
We’d also switch to a trustworthy, audited provider, especially if you’re worried about their data logging and retention practices. Important features you’ll want to look for include IPv6 compatibility, DNS and WebRTC leak protection, and native client apps for your devices. As best you can, we’d also avoid the use of freemium providers, given the limitations and data concerns.
For VPN security, here’s a list of the top 5 secure VPNs.
The majority of VPNs won’t stop cookies from tracking you through a browser. Be wary of cookies, it may be more prudent to switch to a new browser while the VPN is active just in case. (Incognito mode should also be helpful in this instance.)
While few and far between, there are some private browsers worth switching to that won’t track or sell your data at all. It’s best to test out several to find one that fits into your routine.
With a couple of online tools and a bit of additional know-how, you’ll be well equipped when it comes to identifying and fixing any data leaks you encounter while using a VPN. The majority of leaks are easily plugged, although you might need to switch VPN providers if you consistently encounter problems with a specific service. It really shouldn’t be happening often, if at all.
VPN data leaks should be a thing of the past. While that’s not always the case, it’s tough to find many free options that can truly protect your data when matched up with a premium service.
WHAT’S IN THIS REVIEW?
| Cookie | Duration | Description |
|---|---|---|
| __cfduid | 1 month | The cookie is used by cdn services like CloudFlare to identify individual clients behind a shared IP address and apply security settings on a per-client basis. It does not correspond to any user ID in the web application and does not store any personally identifiable information. |
| cookielawinfo-checkbox-advertisement | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Advertisement". |
| cookielawinfo-checkbox-analytics | 1 year | This cookies is set by GDPR Cookie Consent WordPress Plugin. The cookie is used to remember the user consent for the cookies under the category "Analytics". |
| cookielawinfo-checkbox-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-non-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Non-necessary". |
| cookielawinfo-checkbox-performance | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 1 year | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-functional | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-others | 1 year | No description |