October 21, 2021
VPN Protocols: A Complete Guide for 2026
The average VPN has at least a couple of VPN protocols on offer, but what’s the difference [...]
WHAT’S IN THIS REVIEW?
Disclaimer: Partnerships & affiliate links help us create better content. Learn how.
WireGuard might be seen as a fledgling name in the game when it comes to the latest and greatest VPN protocols, but how does it compare when up against the ever-reliable OpenVPN? It might seem like an obvious choice, but it’s not necessarily as cut and dried as you might have expected.
We put together a guide with everything you need to know about WireGuard vs OpenVPN. You’ll see how each protocol compares in terms of speeds, security, and compatibility.
Released in 2020, WireGuard is a popular open-source VPN protocol that aims to improve upon established options like OpenVPN. The latter was released in 2001 and is still going strong in the present day.
WireGuard mixes speed and simplicity, and works out to be one of the more performant protocols thanks to efficient data usage. OpenVPN is more widely available and is better at accessing censored regions.
We’ll run through the key pros and cons of each VPN protocol below, taking into account aspects like speed, encryption, security, auditability, and compatibility. Here’s what to consider when looking at WireGuard vs OpenVPN.
Can be up to 2x faster than OpenVPN
Efficient data usage
No security vulnerabilities
Easy to audit
Less compatibility and support across devices
Privacy issues relating to static IP
Is only used with UDP, so not ideal for avoiding censorship
Better at bypassing censorship
OpenVPN is supported by many VPNs
No security vulnerabilities
Works without logging an IP address
Uses more data than WireGuard
Much slower than WireGuard
Harder to audit
Let’s start with the basics. Virtual private networks (VPN) use protocols to create a stable and secure connection between your device(s) and the internet. A VPN protocol consists of specific rules or instructions that determine how data is routed to and from your device and the VPN server.
There are many protocols designed for different circumstances. Some specialize in privacy while others help maximize connection speeds. Most VPNs offer multiple protocols you can choose from depending on what you’re doing.
Two of the most popular and best protocols today are WireGuard and OpenVPN. We’ve detailed what to expect from each one in the following guide, but first, we’ll start with a brief introduction for each one.

WireGuard is a VPN protocol that was created by Edge Security cryptographer, Jason A. Donenfeld. WireGuard’s first stable release, or version 1.0.0., was on March 29, 2020. In their own words:
“WireGuard is an extremely simple yet fast and modern VPN that utilizes state-of-the-art cryptography. It aims to be faster, simpler, leaner, and more useful than IPsec, while avoiding the massive headache. It intends to be considerably more performant than OpenVPN.”
Jason A. Donenfeld, Edge Security Cryptographer
It’s designed to be a cleaner alternative to older protocols, with just 4,000 lines of code in comparison to the 70,000 found in the open-source version of OpenVPN.
WireGuard uses less power than OpenVPN, is extremely user-friendly, and appears to be just as secure. It’s also much faster. Don’t go jumping ship, though. There are plenty of areas that OpenVPN excels in, too.

OpenVPN was created and released back in 2001 by James Yonan–now the CTO of OpenVPN Inc. It’s used to create secure point-to-point or site-to-site connections in routed or bridged configurations, most notably with client and server applications.
Like Wireguard, OpenVPN is free, open-source software that’s available under the GNU license. OpenVPN works by using the OpenSSL library for encryption and authentication, and it can use either UDP (User Datagram Protocol) or TCP (Transmission Control Protocol) to transmit data from your device to a VPN server.
It might be slightly dated compared to newer protocols, but it’s a tried and tested method that’s undeniably the most popular option by a wide margin. Compared to WireGuard, it’s also more privacy-friendly and is supported by a greater number of VPNs today.
For many users, there’s only one feature that really matters – and that’s speed. Connection speeds are incredibly important for any VPN, especially as data is being funneled to and from their servers before reaching your device. For the user, slower speeds mean more lag and buffering while waiting for services to load, with downloads definitely taking a lot longer.
There’s an obvious winner when looking at the average connection speeds that can be achieved with WireGuard and OpenVPN.
The newer protocol wins easily.
An example of WireGuard’s performance can be found via its website. They provided some older benchmarks relating to speeds, which can be seen below:
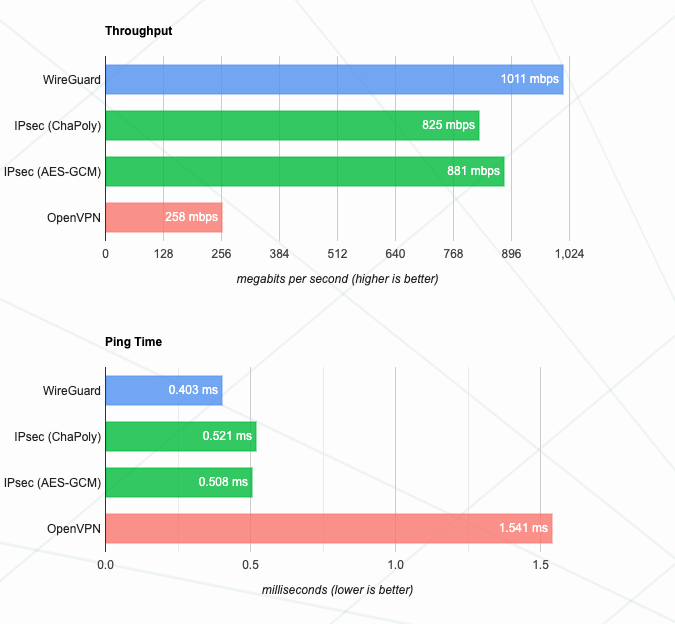
WireGuard notes: “These benchmarks are old, crusty, and not super well conducted. In the intervening time, WireGuard and IPsec have both gotten faster, with WireGuard still edging out IPsec in some cases due to its multi-threading, while OpenVPN remains extremely slow. It is a work in progress to replace the below benchmarks with newer data.”
This can be seen with any VPN service which offers both OpenVPN and WireGuard from the same server locations. The latter is always going to be faster, and can make a significant difference in terms of performance. WireGuard is often 50% faster than OpenVPN.
There was only ever going to be one winner, which makes sense as WireGuard creator Jason Donenfeld got the idea for the service in 2017 when in need of a “stealthy traffic tunneling solution” that could be used during penetration testing.
If you mainly use a VPN for streaming or a VPN for gaming, switching to the WireGuard protocol while online could help you achieve faster connection speeds and reduce lag time. It’s definitely something to consider when shopping for a VPN provider.

It’s a misconception to assume that WireGuard has worse encryption than OpenVPN just because it was built with speed in mind. What it does use is a simpler cryptography system, which does lead to less choice as a result.
WireGuard deploys:
Meanwhile, OpenVPN uses 256-bit OpenSSL encryption. It can use the AES, Camellia, 3DES, CAST-128, or Blowfish ciphers. It’s a reasonably robust selection and is superior to the fixed option given by WireGuard.
OpenVPN has been trusted to do the job for decades. Granted, even though WireGuard lacks the years of auditing that OpenVPN has, WireGuard does handle the security side effectively, too. It’s worth mentioning that there are currently no known security vulnerabilities for either WireGuard or OpenVPN.
Is there any real difference in terms of privacy between the two protocols? One major point of contention is that WireGuard configurations contain a static IP address.
While OpenVPN might not have to log an IP, but WireGuard needs IP addresses to be stored on the server until it reboots. This is an obvious flaw, as an IP address can be matched with the user as a method of identifying them while online.
VPN providers tend to offer a solution to this problem in some shape or form.
For example, Mullvad advocates for the use of the WireGuard protocol with their VPN, but they acknowledge that keeping a static IP address for each device, even internally, is not ideal. Specifically, they note:
“If a user experiences WebRTC leaks, that static internal IP address could leak externally. As another example, applications running on your device can find out your internal IP, and if you’ve installed software that is malicious, it can also leak that information.”
Mullvad automatically replaces the WireGuard keys once a week, while you’ll be able to do so manually whenever you like within the app.
Meanwhile, IVPN apps regenerate a new key pair every 24 hours when using the WireGuard protocol. It also generates new IPs and distributes them to all servers automatically as well. You can see a breakdown of other ways this provider accounts for design issues intentionally used within the WireGuard protocol.
If you plan to use a WireGuard VPN, make sure to check if (and how) they’ve implemented any privacy-related workarounds. And for good measure, you can check it against the WireGuard whitepaper as well to verify that it makes sense for the protocol.
Overall, OpenVPN takes the lead in terms of privacy, while both protocols perform well from a security perspective. Once again, both WireGuard and OpenVPN hold their own.
A VPN will increase the amount of data used while browsing. This is especially important if you’re capped, which is the case for many mobile users.
WireGuard is the winner here, using less data than OpenVPN.
It should also be less taxing on your device due to fewer lines of code, which helps to increase battery life.
Privacy and security are highly important when choosing between WireGuard and OpenVPN. How does their approach affect anything from censorship to auditability?
Combating censorship is one aspect in which OpenVPN clearly has WireGuard beaten. You’ll only be able to use the TCP communication protocol with OpenVPN, which is often used to bypass internet blocks in countries like Russia and China.
TCP ensures a safe and secure transfer of data was initiated. The user receives a confirmation when a sent data packet was properly received before continuing to send the next one. Keep in mind, this protocol can be slow at times, especially when a user is far from a VPN server. (This is another reason why WireGuard has improved performance compared to OpenVPN.)
TCP connections are able to use port 443, which is the same port regular HTTPS traffic uses. It’s unlikely that port 433 will be blocked due to hosting a range of essential online services, s o there’s a clear winner here.
We rely on audits to identify potential vulnerabilities and minimize the potential for risk. It’s the only way you’ll be able to trust that a VPN protocol is working correctly. Both WireGuard and OpenVPN are open-source and auditable, which is a good thing.
On the face of it, OpenVPN is the winner here, thanks to rigorous testing over the past 21 years. However, there are potentially hundreds of thousands of lines of code to sift through, and it takes a lot of time and effort to check everything properly.
WireGuard hasn’t been out for long, but with only 4,000 lines of code, it’s a lot easier to audit when compared to OpenVPN.
Several VPNs have worked to adopt WireGuard as quickly as possible, hoping that the protocol will provide a much-needed boost to speeds and performance. At the lower end, it can make a notable difference, but how does it perform in terms of compatibility?
Don’t be surprised if WireGuard isn’t supported by your favorite VPN, even if you’re using one of the bigger providers. Instead, the likes of NordVPN (NordLynx) and ExpressVPN (Lightway) have opted to build proprietary protocols, which are based on WireGuard but aim to work without posing a risk to privacy.
For example, I ran into issues while attempting to use WireGuard with the otherwise straightforward IPVanish.
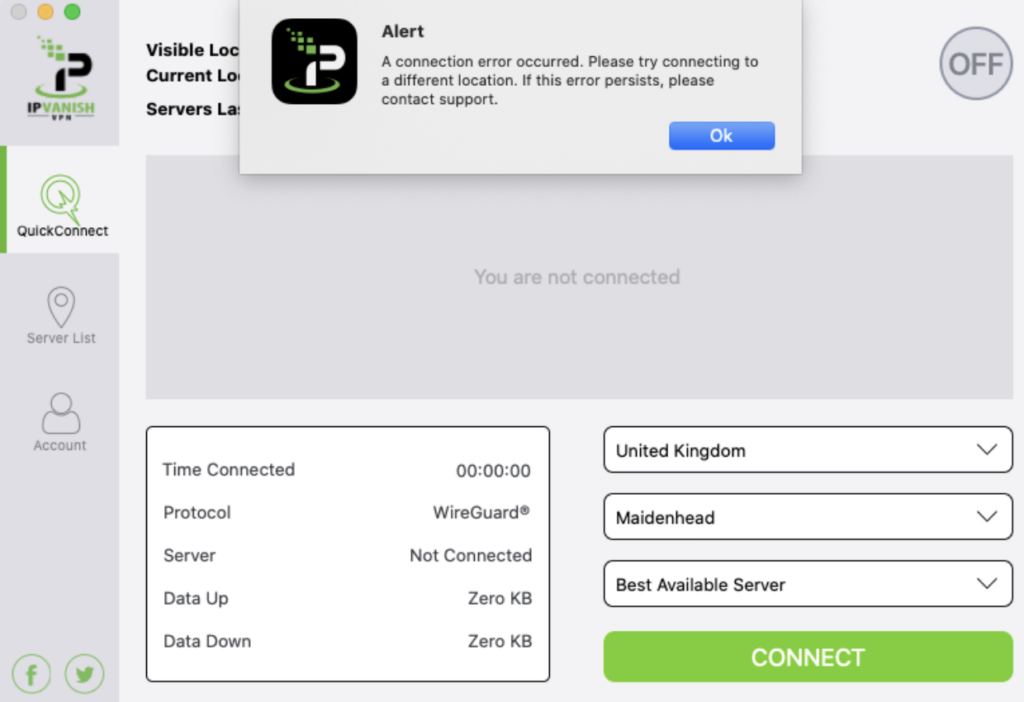
The point is, you might find it difficult to get WireGuard working in the first place, even if you’re sold on what the protocol can do. Below, we recommend a few reputable VPNs that have implemented WireGuard in some shape or form over the past few years.
| VPN | Lowest Price | # of Countries | # of Devices |
|---|---|---|---|
| Private Internet Access | $2.19/mo. | 84 | 10 |
| NordVPN | $3.99/mo. | 60 | 6 |
| Surfshark | $2.49/mo. | 95 | Unlimited |
| CyberGhost | $2.23/mo. | 91 | 7 |
| ExpressVPN | $8.32/mo. | 94 | 5 |
PIA scored highly in our recent review for its performance, network, and trustworthiness mainly. Another perk, though, is that their implementation of WireGuard is now available on all desktop clients and mobile applications.
They note that “Private Internet Access has augmented WireGuard with no logging privacy protections on your VPN servers, so PIA WireGuard users can rest assured that no client-server connections are logged and that their privacy is protected – as is and always will be standard at Private Internet Access.”
Rather than using WireGuard directly, NordVPN has taken a different tack. They created NordLynx, which is built around the protocol with a few differences. However, they do warn users to “please be aware that the WireGuard protocol is still under development. While we are confident in our implementation, WireGuard itself may still contain some unresolved bugs, so use it with caution.”
Surfshark rolled out WireGuard protocol support on Android, Windows, iOS, and macOS in October 2020. Another solid provider that we’d recommend checking out, they assign a dynamic IP address to all WireGuard users. So rather than using a static one, every time you connect to a VPN server using WireGuard, your IP address will be different.
Then there’s CyberGhost. An extremely competent VPN provider, their support pages confirm that WireGuard can be used on every major operating system, including mobile devices:
They’ve donated to the project directly. They also highlight WireGuard’s state-of-the-art cryptography as well as its ability to avoid anti-VPN systems that focus on OpenVPN connections.
Another solid VPN for WireGuard is ExpressVPN. They released Lightway, which is “a brand new, next-generation VPN protocol that will make your connection faster, more reliable, and more secure.” They continue by clarifying that “unlike the off-the-shelf protocols that most other VPN providers use, Lightway was built by ExpressVPN from the ground up to meet your needs, making it easier than ever to protect yourself online.”
It’s not the same as WireGuard, but they’d argue their custom-built tech is markedly better.
Each of the VPNs listed above now offer WireGuard support, while any provider worth your time is likely to offer the OpenVPN protocol.
Examples of VPNs that have both WireGuard and OpenVPN support include:
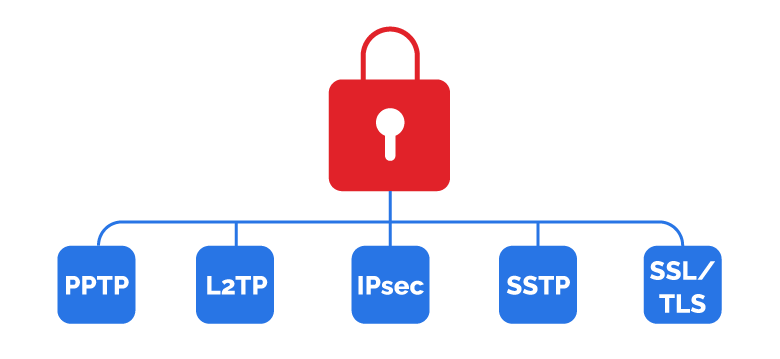
In addition to OpenVPN and WireGuard, there are plenty of other protocols VPNs offer. Each is catered toward specific online activities and is intended to personalize the user experience.
Of course, OpenVPN and WireGuard tend to be the most popular options for a reason, but you can find out more from our complete guide for VPN protocols. The most common ones include:
In addition to OpenVPN and WireGuard, there are plenty of other protocols VPNs offer. Each is catered toward specific online activities and is intended to personalize the user experience.
Of course, OpenVPN and WireGuard tend to be the most popular options for a reason, but you can find out more from our complete guide for VPN protocols. The most common ones include:
Considering all of the above, when should you be using WireGuard or OpenVPN?
Here are some of the more commonly associated questions when looking at WireGuard vs OpenVPN.
Rather than using both protocols at the same time, you’ll be able to select WireGuard or OpenVPN before connecting to a VPN server.
WireGuard is faster than OpenVPN, but it’s not necessarily the quickest protocol overall when accounting for options that don’t use any encryption. However, WireGuard is still the fastest secure VPN protocol overall.
No. WireGuard is a newer protocol that has far less code, built using state-of-the-art cryptography.
WireGuard wasn’t built with anonymity and privacy in mind, preferring to focus on security and speed. As such, we’d opt for OpenVPN.
Neither WireGuard or OpenVPN is a security risk, with both protocols trusted by the majority of experts. WireGuard has the benefit of fewer lines of code which makes it easier to audit, while OpenVPN has been tested rigorously over the past two decades.
Probably not. OpenVPN still has a number of practical uses, such as with TCP connections.
Not necessarily, and many experts would consider OpenVPN to be the safer option. However, WireGuard is simpler by design, with less code to attack, and it’s easier to audit. Both are safe VPN protocol solutions.
It’s easy to think of OpenVPN as being on its way out, especially when compared to an up-and-coming protocol that many industry experts now favor. However, WireGuard is still somewhat experimental, and it isn’t as widely available as of yet.
In terms of WireGuard vs OpenVPN, asking which one is better isn’t really the ideal way to look at it. Instead, consider your needs. Is speed of utmost importance to you? Or, do you care most about privacy or device compatibility? Figuring out exactly what you want from a VPN protocol first will help you to make a decision.
Either option is solid from a privacy and security perspective, although WireGuard falls behind in terms of compatibility. It’s to be expected, and the scale should be balanced more evenly in the future as it becomes more widely adopted.
Overall, you’ll be able to boost your online privacy drastically with the use of a fully audited VPN service. For OpenVPN, we recommend testing out Private Internet Access, whereas NordVPN might be ideal if you want to learn the ins and outs of WireGuard on a range of devices. It ultimately comes down to preference.
WHAT’S IN THIS REVIEW?
| Cookie | Duration | Description |
|---|---|---|
| __cfduid | 1 month | The cookie is used by cdn services like CloudFlare to identify individual clients behind a shared IP address and apply security settings on a per-client basis. It does not correspond to any user ID in the web application and does not store any personally identifiable information. |
| cookielawinfo-checkbox-advertisement | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Advertisement". |
| cookielawinfo-checkbox-analytics | 1 year | This cookies is set by GDPR Cookie Consent WordPress Plugin. The cookie is used to remember the user consent for the cookies under the category "Analytics". |
| cookielawinfo-checkbox-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-non-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Non-necessary". |
| cookielawinfo-checkbox-performance | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 1 year | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-functional | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-others | 1 year | No description |