October 14, 2021
Cybersecurity Awareness Month: How to be Cyber Smart
As technology becomes more sophisticated, cyber attacks are trailing closely behind. That’s why [...]
WHAT’S IN THIS REVIEW?
Disclaimer: Partnerships & affiliate links help us create better content. Learn how.
Cyber attacks are an ever-growing concern for individuals, small businesses, and large corporations all around the world. In fact, cybercrime is estimated to cost about $10.5 trillion annually by the year 2025! If that doesn’t make your jaw drop, then I bet the true-crime cyber attack stories I’m about to share will.
Unknowingly, many individuals and businesses are digging a deeper hole of vulnerabilities within our digital world. Think about it—a great number of us are connecting our devices to unsecured networks at home, local coffee shops, and coworking spaces. And hackers are at the frontline targeting connected devices with poor cybersecurity. Each incident below not only demonstrates the importance of cybersecurity but also shows how smart cyber criminals can be to get what they want.
Without further ado, queue the ominous true-crime music…

You read that right—5 times in 4 years! You think after the first data breach T-Mobile would have learned its lesson. But due to lackluster cybersecurity, their system has been hacked more times than a telecom giant would like to admit.
The first T-Mobile cyber attack was confirmed in August 2018, when hackers exploited a vulnerable API (application programming interface) by breaching T-Mobile’s database. The attack impacted about 2 million T-Mobile customers—out of their estimated 75 million total users at the time—with their names, zip codes, phone numbers, email addresses, and account numbers potentially exposed. Thankfully the exploited API was not linked to payment data, passwords, and social security numbers.
T-Mobile was hacked for the second time in November 2019. This data breach affected over 1 million of its customers with their personal data exposed to a cyber criminal. The data exposed included names, billing addresses, phone numbers, account numbers, and plan features. So similar to the attack in 2018, sensitive information like social security numbers and credit card numbers were not stolen. Account hijacking was possible with the exposed data, so changing account passwords was recommended for the affected customers.
Only 6 months after the 2019 incident, a sophisticated cyber attack breached the email accounts of T-Mobile employees. T-Mobile didn’t disclose the number of users affected but did confirm that social security numbers and credit card numbers were not stolen. This marks the third breach against T-Mobile’s database which resulted in user names, phone numbers, account numbers, billing addresses, and plan features being exposed to unknown hackers.
2020 was a tough year for all of us—especially for T-Mobile who had not one but two cyber attacks. About 200,000 users were affected by data breach #2 in 2020. The exposed data included their phone numbers, call records, and the number of lines on user accounts. Once again, it’s a miracle credit card numbers and social security numbers were not stolen. However, it’s obviously concerning that this is a recurring theme for T-Mobile.
The most recent T-Mobile data breach was by far the largest and most appalling cyber attack they experienced. About 47 million current, prospective, and former customers were affected. Their names, birthdays, social security numbers, and driver’s license information were all accessed by a malicious hacker. That’s more than half of their customer base. This attack was discovered when the hacker was attempting to sell $270,000 worth of sensitive information in an online forum. T-Mobile confirmed that the access point of the breach was immediately closed off and is further investigating the incident.
In 2020, hackers attempted to attack top officials of the World Health Organization (WHO) with phishing emails. These emails included a malicious link to download malware onto their devices. Fortunately, the WHO was not hacked but users of 4chan, an internet forum for alt-right groups, exposed 2,000 passwords they claimed were for WHO employee email accounts. It’s believed this was done to sabotage the credibility of the WHO’s public health guidelines regarding the coronavirus.
Hackers were also making an effort to impersonate WHO employees by sending phishing emails to the public. These messages asked for donations to a fraudulent COVID-19 relief fund, instead of the real COVID-19 Solidarity Response Fund.
PRO TIP: Always keep an eye out for phishing with suspicious links and/or requests. Do not click links, download attachments, or comply with their requests.
In 2020, hackers posted fake tweets from prominent Twitter handles, including Elon Musk, Apple, and Jeff Bezos. Hackers were able to compromise their login credentials, pose as them, and scam followers in a “get rich quick” scheme.
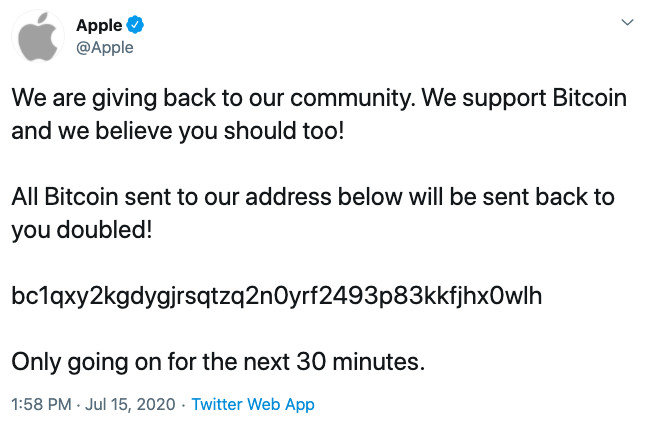
Unfortunately, many people fell for this scam and over 400 bitcoin payments were transferred. The cyber criminals acted fast and started to transfer the cryptocurrency to an unknown address to exchange it for cash. In total, these payments reached a cash value of about $121,000. The obvious moral of the story is that if it’s too good to be true, then it probably is.

Due to a previous cyber attack on the Microsoft Exchange platform, Acer also fell victim to a hack because of a vulnerability found in Microsoft’s ProxyLogon. The cyber criminals responsible are known as REvil. It’s a group notorious for targeting companies with poor cybersecurity and making costly ransom demands. REvil managed to steal Acer’s identity and data through a ransomware attack, which encrypted their files and made their system inoperable. The stolen data was then released on a data leakage site, called Happy Blog. REvil threatened to keep the assets published until they paid a ransom of $50 million by a specific date. This stands as the largest ransom recorded in history!
The COVID-19 pandemic led to the highest record of unemployment claims after the US government issued a lockdown to prevent the virus from spreading. Almost 23 million claims were filed in May 2020, but the FBI found an alarming amount of these were fraudulent. Cyber criminals stole taxpayer information through phishing emails, dark web purchases, and cold-calling scams to use for impersonating victims and filing false unemployment claims.
In hopes to keep taxpayers safe, the IRS releases the Dirty Dozen—an annual list of scams for Americans to beware of. In the 2020 report, the IRS listed numerous scams, including fake charities, social media scams, ransomware, and more. Mainly, it was encouraged for Americans to be on the lookout for threats during the pandemic as more cyber criminals were aiming to target vulnerable devices.
In February 2021, a hacker attempted to poison the 15,000 people of Oldsmar, Florida by raising sodium hydroxide levels in their water to 100 times more than the normal level. The hacker was able to break into the system of the water treatment plant and take control of a plant operator’s computer. The plant operator witnessed his cursor moving and using various software functions to control the city’s water treatment process. Thankfully, as soon as the hacker exited the system, the operator was able to bring the sodium hydroxide levels back to normal.
The Pinellas County Sheriff ensured that if the plant operator didn’t respond swiftly to this incident, certain system safeguards would have caught the high levels of sodium hydroxide and kept the poisoned water from entering the homes of Oldsmar. Still, this cyber attack brought on national attention and urged cities to be on alert for any unusual activity across their water treatment systems.
A Russian group, known as the DarkSide, was able to take down America’s Colonial Pipeline system—the largest fuel line that stretches across numerous southern and east coast states. This cyber attack caused fuel prices to significantly rise in a matter of day. It also led to outrageously long lines at gas stations, where many were pumped dry.
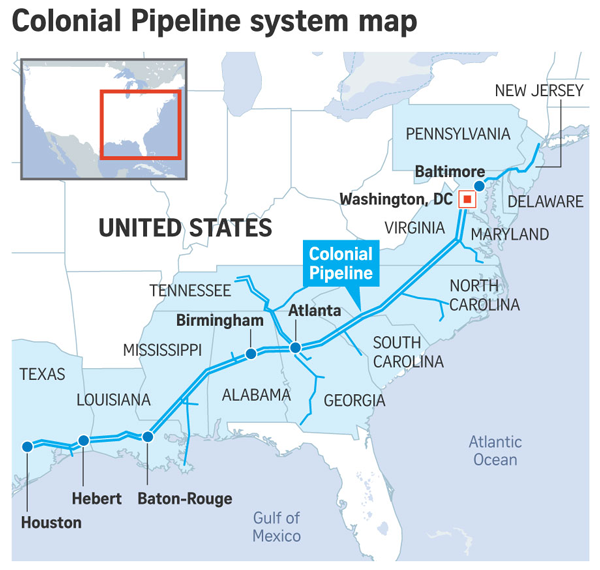
The Colonial Pipeline system was using a VPN but not one protected by multi-factor authentication. So, the hackers were able to breach the system with only a username and password. It’s unclear if DarkSide was able to obtain the login credentials through a previous hack or repeatedly tried password combinations to finally guess the correct one.
PRO TIP: If multi-factor authentication is a login option, always enable it.
Only an hour after the breach, the hackers shut down the Colonial Pipeline and threatened to leak about 100 GB worth of stolen data if a $4.4 million ransom wasn’t paid. The company running the pipeline complied with their request and the pipeline resumed service 5 days after it was shut down on May 7, 2021.
It’s scary that even well-established companies and organizations make the headlines as cyber attack victims. This can understandably make us question the trust we put into these systems and the people that run them. That’s why it’s extremely important to be cyber smart and enable personal cybersecurity measures like using a secure VPN or password manager for online tasks. This will not only help ensure the safety of your data and identity but also keep you one step ahead of dangerous hackers on the prowl.
| Cookie | Duration | Description |
|---|---|---|
| __cfduid | 1 month | The cookie is used by cdn services like CloudFlare to identify individual clients behind a shared IP address and apply security settings on a per-client basis. It does not correspond to any user ID in the web application and does not store any personally identifiable information. |
| cookielawinfo-checkbox-advertisement | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Advertisement". |
| cookielawinfo-checkbox-analytics | 1 year | This cookies is set by GDPR Cookie Consent WordPress Plugin. The cookie is used to remember the user consent for the cookies under the category "Analytics". |
| cookielawinfo-checkbox-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-non-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Non-necessary". |
| cookielawinfo-checkbox-performance | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 1 year | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-functional | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-others | 1 year | No description |