October 18, 2021
50 VPN Statistics & Key Trends [2022]
This year alone, VPN usage has increased drastically, many services have vastly improved, and the [...]
WHAT’S IN THIS REVIEW?
Disclaimer: Partnerships & affiliate links help us create better content. Learn how.
Shadowy surveillance alliances are more common than you might have thought, and cover vast swathes of the globe. SIGINT and COMINT are forms of surveillance that are common and most relevant to online privacy – or lack thereof.
Signals intelligence (SIGINT) is a popular method of information-gathering using the interception of signals, including any electronic forms of communication. This typically refers to electronic transmissions that are collected by ships, planes, ground sites, or satellites.
Communications intelligence (COMINT) can be gathered via phone calls, text messages, or online interactions, including anything from search functions to other forms of intercepted internet-based comms.
Both directly tie into the Five Eyes (FVEY) surveillance alliance, which is one of the most comprehensive spy networks that has ever been made public, thanks to the Edward Snowden leaks back in 2013.
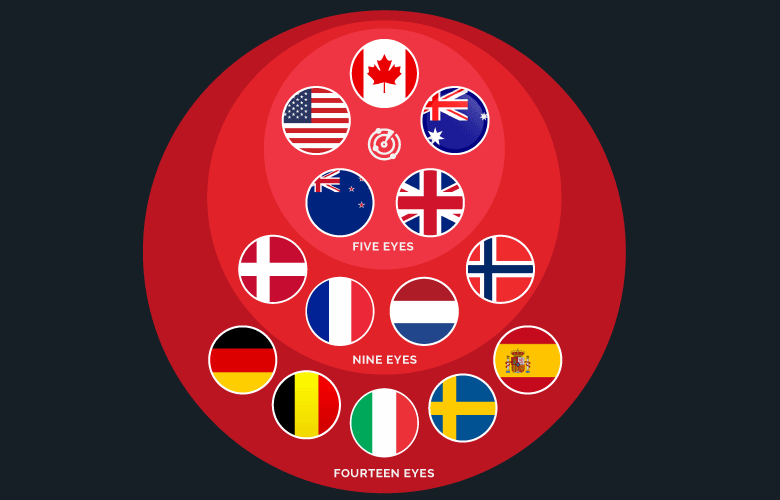
The point is, FVEY is a big deal if you’re interested in online privacy. This is especially true as it’s tough to avoid its large jurisdictional reach. Then there are the expanded 9 Eyes and 14 Eyes alliances, which include more nations dotted around the globe.
The ability to provide privacy is a key feature of a secure VPN, and it’s a viable method to ensure that your data remains ungathered.
Here’s everything you need to know about the Five Eyes (FVEY) surveillance alliance and how you can avoid their prying eyes as best you can.

In the words of the UK Defence Journal: “The Five Eyes brings the UK, the United States, Canada, Australia, and New Zealand into the world’s most complete and comprehensive intelligence alliance.”
Originally conceived during the latter stages of WW2, the signal intercept (SIGINT) networks of the UK Government Communications Headquarters (GCHQ) and the US National Security Agency (NSA) teamed up following the prospect of a Cold War with Russia.
This was later expanded to include a trio of commonwealth countries, which also happened to be strategically placed around the globe.
Each of the FVEY countries (United States, Canada, Australia, UK, New Zealand) share a common language that makes it easy to send intelligence quickly. It’s also an alliance that conveniently makes up the majority of key regions in the Anglosphere.
They are thought to share raw intelligence, funding, technical systems, and personnel.
The makeup of the FVEY alliance has remained the same ever since. This is despite recent proposals that would see Germany, India, Japan, and South Korea join the network.
We’d be especially wary of signing up with a VPN service based in any of the 14 Eyes nations if you’re solely interested in privacy. After all, if they manage to get access to your data, it’ll be freely available to be shared with any other countries within the alliance.
This is why it’s always a good idea to pay attention to the jurisdiction of a VPN. Make sure you know the answers to the following questions when selecting your provider:
As the name implies, there are five countries that make up the original FVEY alliance. It’s worth noting that each member of the pact is rumored to be tasked with collecting intelligence in a different part of the world.
As for the name itself, it’s due to their reports being for “US/UK/CAN/AUS/NZL Eyes Only,” which was later shortened to FVEY.
The United States and the UK formed an alliance in 1946. It consists of a series of bilateral agreements on surveillance and intelligence-sharing. The original United Kingdom-United States Communication Intelligence Act (UKUSA) agreement has since been declassified and can be viewed online.
A large number of VPN services are based in the United States. This is a major drawback if online privacy is your main aim. The same is true for the UK, so be especially wary if you’re unsure of where a provider is headquartered.
Canada was the first nation to join the UK/USA alliance just two years after it was formed.
They were given special provisions, even in place of other nations within the Commonwealth. As such, Canada and the CSIS should be seen as major FVEY partners.
Australia joined along with New Zealand in 1956, representing another strategic geopolitical hub. However, the secret agreement was not officially acknowledged though its existence was rumored about since the 1980s. It was eventually declassified in 2010.
In an ongoing theme, New Zealand was the last of the “UK/USA-collaborating Commonwealth countries” to be given an invitation to FVEY.
Nine eyes is an expansion of the original FVEY agreement, in a second-tier with more restrictions in place in terms of the information shared. Of course, this collection of countries also includes the FVEY agencies mentioned above.
The 2013 Snowden leaks “revealed that Denmark has a closer working relationship with the NSA than many other European countries, including neighbors Sweden and Germany.”
France isn’t a member of the Five Eyes group, but the nation enjoys close relations with both the U.S. and the UK, according to former French Air Force chief of staff André Lanata in an interview back in 2017.
Edward Snowden dubbed the Dutch “the Surveillance Kings of Europe” back in 2017, due to their strong ties to FVEY nations.
The final member of the 9 Eyes alliance is Norway. Once again, the Snowden leaks give an insight into the workings of various agencies, according to minutes from Britain’s GCHQ intelligence agency that were obtained by the Guardian in 2013. They noted:
“The NSA’s relationship with the French was not as advanced as GCHQ’s … the Germans were a little grumpy at not being invited to join the 9-Eyes group.”

As well as the 9 Eyes countries, a third-tier exists, expanding the total of nations to 14. Once again, intelligence is likely to be more restricted compared to FVEY or 9 Eyes. However, little is known about the exact arrangements.
Formed in 1982, it’s alternatively known as SIGINT Seniors, with a European branch that was formed amid the Cold War. It was expanded to 14 nations following the 9/11 attacks, with Germany, Belgium, Spain, Sweden, and Italy signing up.
Rather than a treaty, it’s believed to be an arrangement between the countries mentioned above.
If you’re keen to steer clear of 14 Eyes nations, we’ve listed five great VPNs below that are based outside of their jurisdictions.
NordVPN is a privacy-focused option that is based in Panama, owned by Tefincom S.A. They have a variety of additional security features including the proprietary protocol NordLynx, making it a viable choice.
They’ve been audited by the likes of VerSprite who have verified their logging claims, and they have a strong selection of high-speed servers.
DoubleVPN routing, a kill switch, and their CyberSec ad-blocker offer further protection, while Onion over VPN gives you all the advantages of The Onion Router (Tor) combined with the extra security of a VPN tunnel.
CyberGhost is headquartered in Romania, although they’re owned by Kape Technologies, which is based in the UK. They say:
“Back in 2006, the Romanian Constitutional Court refused to adopt the EU Data Retention Directive, calling it unconstitutional. In 2011, the Romanian Senate unanimously rejected the new draft law on the retention of data. According to Romanian law, we are under no obligation to keep tabs on our users. This enables us to strictly enforce our no-logs policy.”
CyberGhost offers built-in features like IPv6, DNS, and WebRTC leak protection, while you’ll be able to pay for the service with cryptocurrencies.
The British Virgin Islands might sound like it’s affiliated with the UK, but they have their own set of privacy laws which make it a great location to base a VPN service.
SurfShark servers passed an independent infrastructure audit in May 2021, this time courtesy of Cure53.
The VPN benefits from a large network of over 3,200 servers that are backed by AES 256-bit encryption, multi-hop protection, and a zero-logs policy. It’s another solid choice from a privacy perspective.
From the team behind ProtonMail, ProtonVPN is another viable option for users who place an emphasis on privacy. The developers created ProtonVPN to ‘protect the journalists and activists who use ProtonMail’.
Based in Switzerland, it’s worth mentioning that the nation has been known to cooperate with 14-Eyes countries via the courts. However, ProtonVPN does operate with a strict no-logs policy.
Their Secure Core servers route user traffic via privacy-friendly countries like Switzerland and Iceland, while it allows for Tor over VPN, and only uses ciphers with Perfect Forward Secrecy.
Last, but by no means least, PureVPN is the first provider with an ‘Always-On audit’.
This sounds fairly gimmicky, although it means that auditing firm KPMG can conduct a thorough surprise review of PureVPN’s processes and servers at any time without prior notice.
They accept various forms of crypto as payment. And, they offer numerous paid extras, such as a Dedicated IP, port forwarding, and DDos protection. After spending over fourteen years in Hong Kong, PureVPN moved Headquarters to the British Virgin Islands in 2021.
Here are some of the more common questions associated with the various shared intelligence agreements discussed above.
Agencies simply can’t be trusted not to share your data, and little is known about exactly what they do with the information collected. It’s tempting to think that intelligence collected is solely used to catch “bad guys,” but that’s unlikely to be the case.
As for providers, Riseup, IPVanish, and HideMyAss have all been forced to hand over user data in the past, with the first two based in the US, and HMA found in the UK.
The various alliances allow agencies to cover a large landmass, and they’re able to communicate and identify threats rapidly. Of course, there’s no telling the real scope of their efforts, while it’s worrying from a privacy point of view.
A VPN masks your IP address, making it harder to track your online movements. Instead, all data to and from your device will be routed through an encrypted tunnel.
This data should be disposed of by the VPN service, which is why it makes sense to pay attention to their logging policy before signing up. If they have no logs, they’ll have nothing to hand over, even if court-ordered to do so. Regardless, it’s still better to avoid 14 Eyes countries if possible.
Japan has been receptive to the idea of joining the original FVEY alliance, possibly due to geopolitical issues in the region.
Former Japanese Defense Minister Taro Kono gave an interview in August 2020 where he noted the country was eager to expand cooperation with the Five Eyes intelligence-sharing countries, expanding on currently existing frameworks.
Israel, Singapore, and South Korea have also been touted as potential additions to the network.
It’s not just a matter of privacy; it also raises questions relating to oversight and a lack of rules and regulations in terms of the data agencies collect. Privacy International explains:
“The Five Eyes intelligence-sharing arrangements are shrouded in secrecy, allowing for arbitrary or unlawful intrusions on the right to privacy which circumvent domestic legal restrictions on state surveillance. There is no domestic legislation governing intelligence-sharing, meaning that many of these arrangements lack legal basis and therefore democratic legitimacy.”
WHAT’S IN THIS REVIEW?
| Cookie | Duration | Description |
|---|---|---|
| __cfduid | 1 month | The cookie is used by cdn services like CloudFlare to identify individual clients behind a shared IP address and apply security settings on a per-client basis. It does not correspond to any user ID in the web application and does not store any personally identifiable information. |
| cookielawinfo-checkbox-advertisement | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Advertisement". |
| cookielawinfo-checkbox-analytics | 1 year | This cookies is set by GDPR Cookie Consent WordPress Plugin. The cookie is used to remember the user consent for the cookies under the category "Analytics". |
| cookielawinfo-checkbox-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-non-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Non-necessary". |
| cookielawinfo-checkbox-performance | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 1 year | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-functional | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-others | 1 year | No description |